| Q: |
Do I have to have a permanent internet connection to
use the software? |
| A: |
No. |
| Q: |
How long have you been in business and how many customers do
you have? |
| A: |
We have been in the programming/consulting business for over
15 years and have at various times had relationships with hardware support
companies. We have had customers running on this and previous versions
since mid 2000. We do not provide any information about our customers.
Sorry. |
| Q: |
I have a 13 person office. What would a typical setup
look like? |
| A: |
Something like this:
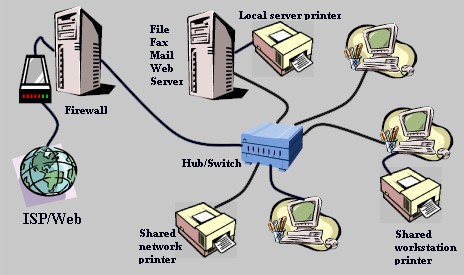
The Firewall would have two network cards; 1 goes to the same hub (switch) as the
workstations using standard ethernet cable, and the other goes to the
router/satellite/DSL modem. The Server should have our Firewall License
installed to protect your internal network. Another server provides all other
network services
like mail, web, fax, file server (with print services), etc. and those servers
are connected to
the same hub as the user workstations. Although not recommended, you could
combine the firewall and the "services" server on the same pc. The
reason the firewall should be separate is to make it harder for a hacker to do
damage in the event that someone did get through.
|
| Q: |
I have a 230 person office with an existing
network with a permanent T1 to the internet. How could I use your software? |
| A: |
Assuming that you already have a decent firewall to protect
that network, you could use our software to replace your existing file, mail,
fax, and web server(s).
The next release due out soon will allow our firewall to act as
an internal and external firewall. This will allow you to use our firewall
internally to control traffic and security between subnets. Larger companies
like yours could benefit from this new feature.
Our web server uses the latest fully featured Apache
SSL server software and should work quite well for most companies. If you
have a high volume requirement you may require a more advanced web
server than we currently offer but our other servers are more than capable of
handling an office of your size. You would require, and probably already
have, fairly decent hardware. Our software would help you get the most out
of your existing equipment, especially if you are due to upgrade your servers.
|
| Q: |
Your software runs on Linux right? Do you provide source code
since it is a GNU type system? |
| A: |
Yes and no. We used the
RedHat distribution originally. In order to provide just the basics and to
improve security, we normally don't even allow user logins on the server
installation. The source code would be useless to have on the server but
is readily available via RedHat. The source code for our program is not
distributed for security reasons but could be made available under certain
circumstances. |
| Q: |
Why RedHat? |
| A: |
We liked
it! You should understand that Linux distributions are really only
different in the packaging. RedHat and others have modified some key
elements but generally just provide their particular setup and management tools
along with their opinion on how the system should be 'structured' as far as
directories, partitions, etc. RedHat came with a fairly lean, secure,
robust kernel (main brain program for the operating system). Other than
applying patches, we have no need to change the way they do things.
Performance tuning, web mail, and VPN services require significant kernel
changes and is the primary reason why we call our version by a different name. |
| Q: |
Why is your software any better than some of the other 'server' packages out
there? |
| A: |
The primary difference between us and most of the rest
is that we came from a Microsoft environment and know that a very large
percentage of companies out there need a specific type of system. Our
software works on the most common type of hardware (IDE, ethernet, Intel, etc.)
and is structured so that you really don't need to know Linux to take advantage
of what most companies need and Linux provides exceptionally well despite an
incredibly low cost. Customers generally don't care how it works,
they just want it to work consistently without having to deal with the
details. We take care of the details. |
| Q: |
I'm using the
Firewall & Mail server on one box. Why do I have to setup the Mail screens
but also have to go to the Admin page to turn services on and off? |
| A: |
The Firewall Mail tab is where you setup firewall 'rules' to what is allowed to
pass through the firewall. This doesn't control services running on the
Firewall. The setups on the Admin page allow you to actually turn on and
off services running on that box. |
| Q: |
The server clock doesn't
seem to recognize daylight savings time |
| A: |
Not yet. We are
working on it. You will have to use the Admin page to set the system time
when daylight savings rolls around. We are also working on a time server
option that will let you sync all of your servers to a standard internet time
server. Currently, the firewall just allows time server packets to pass
through if you give it the IP numbers that another internal computer may be
trying to use. |
| Q: |
We have a Mail server and a separate File
server. Why do we have to enter all the user accounts on each
server? You already have them on one so why not just copy them to the
other? |
| A: |
We considered that for quite a while. We are
working on a new feature that will allow you to selectively copy users from one
of our servers to another. The reason we don't 'copy' them from one to the
other is because most companies don't want this. Specific users are
allowed controlled access to specific servers and the services they offer.
In a multi-server larger office this is particularly true. In a small
multi-server office there is a need to have the copy feature and is the reason
we will be including it in a near future release. |
| Q: |
We already have a mixed bag of Novell and NT
servers. Can I use your software without dumping my investment in
what I have? |
| A: |
Absolutely! We have servers running in an office that
runs Novell, NT, a proprietary Unix system, DOS, Microsoft Windows,
Macintosh, dumb terminal workstations, and
more. That's one of the benefits of Linux over some of the
others. It gets along with practically everything. The advantages
using our servers to either replace or assist is that you can either start
moving away from those servers that aren't doing what you need or allow
you to add abilities that you just can't get with the others (at least for
a reasonable price). |
| Q: |
I've heard about a lot of programs lately that have
backdoors or spyware stuff in it that sends information without
authorization. Does your program send anything out without
permission or is there backdoors that let you or anyone else have
access? How can I believe you? |
| A: |
Our programs do not send anything to anyone without your
permission. In fact, the only way information leaves your server is
by someone you have allowed access, and that includes us. Our installation
CD does install quite a large number of GNU/GPL software that could
possibly have such features but we are always on the lookout for programs
like that and would immediately blacklist them when found. We are
not aware of any way to gain 'backdoor' access to our program or to the
server via our program. Access to the server must be granted by you
using the 'Admin' configuration screen. In order for us to do
auto-updates to your server via the internet, we must have your current
admin password and be allowed access via your firewall. There is no way to
access the server using our program without having a valid username and
password and you must choose a good password and share it with us for
auto-updates.
We stake our reputation on our word. If that isn't sufficient, at
your expense we would allow a third party to examine the source code to
verify what we say is true (Third party must sign a non-disclosure
agreement).
|